http://repos.fedorapeople.org/repos/devos/wireshark-gluster/.The current packages can not only detect most of the Gluster traffic as explained in a previous post, but also display some of the more complex XDR structures used.
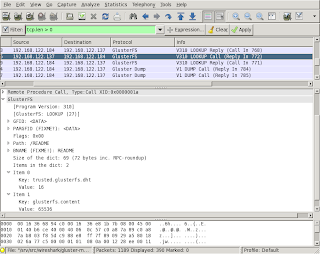
A screen shot of one example with Wireshark on Fedora 16:
Some of the captions in the display contain
FIXME or similar notes. These are mainly reminders for myself, but also should be helpful for people trying the packages and suggesting improvements. Just by reading the Gluster sources, it is not always clear what the specific fields in the communication should be called in a user friendly way.There is an open invite to improve the decoding done by the dissector. The code is (hopefully) easy to understand and should provide a low entry level. There are quite some notes in the code where it needs improvement (search for
FIXME in the main .c file).Coding is one thing, documenting the protocol is something that is closely related to the Wireshark dissector. How would reading traffic help, when you can not check if what you see is what should be happening? A start with documenting this can be found in my github repository which contains the latest sources.